Sliver C2: Pentesting and Evasion (Course review)

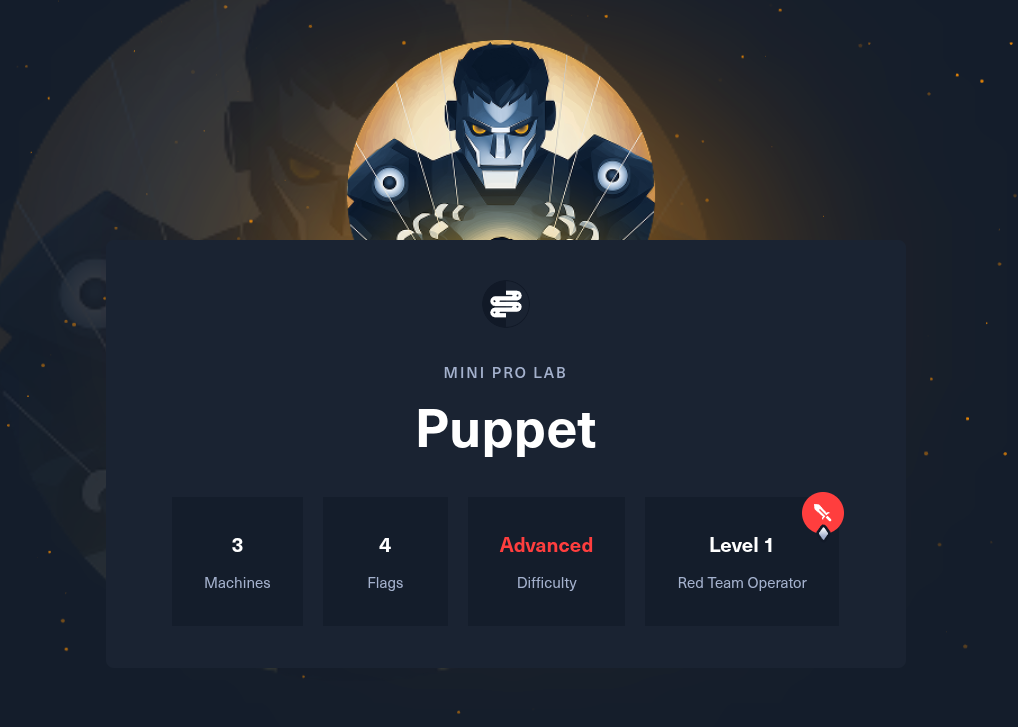
Following my CPTS certification, I started experimenting with some HackTheBox Pro Labs because I wanted to work with more complex networks, especially since VulnLabs was beginning to roll out. However, before purchasing a Pro Labs bundle, I wanted to try a free one first, which led me to completing Puppet.
Now, without giving too much away, the lab focuses on using Sliver, a newer C2 framework.
Sliver is a powerful command and control (C2) framework designed to provide advanced capabilities for covertly managing and controlling remote systems. With Sliver, security professionals, red teams, and penetration testers can easily establish a secure and reliable communication channel over Mutual TLS, HTTP(S), DNS, or Wireguard with target machines. Enabling them to execute commands, gather information, and perform various post-exploitation activities. The framework offers a user-friendly console interface, extensive functionality, and support for multiple operating systems as well as multiple CPU architectures, making it an indispensable tool for conducting comprehensive offensive security operations.
I was very interested because I wanted to work with a C2 framework that I could leverage in the future without paying a boatload of money for a platform like Cobalt Strike. After completing the lab, I was hooked, and I wanted to learn even more about Sliver. During my Google-fu, I discovered that Tyler Ramsbey had created a course on Sliver on his platform, hacksmarter.org.

Sliver C2: Pentesting and Evasion
I already knew of Tyler because I came across him during my OSCP preparation through the YouTube video below, which led me to keep an eye on his work.
Tyler Passing OSCP
I knew about his platform, but honestly I wasn’t too interested at first since a lot of the content was geared more toward a beginner audience. However, when I saw the Sliver course, I thought it was a great opportunity to check out his platform and pick up some Sliver skills.
Course Review:
I won’t cite everything from his site word for word; however, one item I wanted to call out is the initial description:
Become an operationally capable Sliver C2 operator.
A professional, lab-driven training program that moves you from fundamentals to full-scale C2 operations — with hosted labs, instructor demos, real-world workflows, quizzes, and a capstone that proves you can execute the entire attack lifecycle.
The course is divided into eight sections that progressively build on one another, each accompanied by labs. It includes 80 hours of lab time, which is more than enough.
I won’t get into any details whatsoever, as Tyler worked hard on this course and I don’t want to give anything away for free. However, I will say that, in my opinion, about 80% of the course is geared more toward beginners, while the remaining 20% dives into intermediate and advanced topics.
Personally, I completed the course in about 2.5 days, and I had no issues accessing the labs or following the material. However, one thing I want to point out is that I have a bit more experience in most of these topics, so I was able to breeze through the labs.
Holistically, the course was great, although it did feel a bit short—mostly because of the speed at which I was able to work through the sections. I think a beginner in the offensive security field with no C2 experience would benefit greatly from taking this course, as it builds strong foundational skills. However, this is not a substitute for an entry-level course such as TCM Security’s PEH. Tyler even points out that he recommends having PJPT level knowledge before taking this course.
Closing thoughts/Feedback:
I know this review is a bit vague, but I avoided giving specific details about the sections so as not to reveal any course material. However, I think this is a great course for beginners. I honestly can’t recommend it for anyone who already works with Sliver or a similar C2 framework.
With regard to feedback, I’ve already provided Tyler and his team with direct comments, but I’ll add some general points below:
- The labs are a bit too guided.
- Some labs are redundant or repetitive.
